Privacy and Security at RegScale
We never compromise on meeting industry-leading privacy and security standards.
Trust RegScale to Empower your Security Strategy
While many solutions may seem secure on the surface, they often possess vulnerabilities within the network. RegScale has implemented cutting-edge Zero-Trust security methodologies to ensure comprehensive protection throughout.

Persistent Cloud Container Reconstruction
Say goodbye to patching. We rebuild new every time we update, eliminating any zero-day threats while rotating certificates automatically and leaving adversaries to try and hit a moving target.

Continuous Monitoring
We monitor all traffic flow 24/7/365 with cutting-edge SIEM/SOAR solutions designed to protect and automatically react to any threat to data in the environment.

Defense-In-Depth
We deny all traffic by default, eliminate open ports, and make it extremely difficult to move laterally by micro-segmenting application services, using serverless networking technology.
Trusted by the most secure and compliant organizations on the planet
Compliance is at our Core
Though a small startup, RegScale has already obtained certifications across notably complex compliance frameworks, including SOC 2 Type 2 and FedRAMP High.

SOC 2
TYPE 2Achieved in January 2024. We embraced the opportunity to showcase how our own Continuous Controls Monitoring platform helped us obtain the SOC 2 Type 2 certification with significantly less time and effort. Using our CCM platform, we compressed roughly 400 hours of manual work into fewer than 25 hours over a six-month period.

FedRAMP® High
AuthorizedFedRAMP High Approved in June 2025 with agency sponsorship from DHS. We achieved authorization 3-4x faster and 50% cheaper than the industry average using our automation-driven platform.

DoD IL5
In ProcessThe DoD Cloud Computing Security Requirements Guide (DoD CC SRG) outlines the security model and requirements by which DoD will leverage cloud computing along with the security controls and requirements necessary for using cloud-based solutions. The DoD CC SRG includes DOD Impact Level 5 (IL5), outlining Higher Sensitivity Controlled Unclassified Information (CUI), Mission Critical Information, and National Security Systems.

TX-RAMP
AuthorizedRegScale is TX-RAMP Level 2 certified, the highest authorization level under the Texas Risk and Authorization Management Program. This certification confirms that RegScale has undergone an independent security assessment and meets the full NIST SP 800-53 Moderate control baseline, making it approved for use with sensitive data by Texas state agencies and higher ed institutions.

SBOM Core Application
Software Bill of Materials (SBOM) for the Core RegScale Application is a nested inventory for software, a list of ingredients that make up its components. RegScale believes SBOMs are foundational elements necessary to provide greater security and trust in all technology. Submit your request for the SBOM of the Core RegScale Application.

SBOM CLI Automation Platform
Software Bill of Materials (SBOM) for the RegScale CLI Automation Platform is another nested inventory for software. RegScale believes SBOMs are foundational elements necessary to provide greater security and trust in all technology. Submit your request for the SBOM of the RegScale CLI Automation Platform.

CSA STAR Valid-AI-ted Solution
RegScale achieved Cloud Security Alliance (CSA) STAR designation as a Valid-AI-ted solution in Sep 2025 after earning a 97.7% score on its Consensus Assessments Initiative Questionnaire (CAIQ). The designation highlights RegScale’s commitment to security excellence, trust, and innovation as the company advances its mission to deliver living, intelligent compliance powered by AI.

CSA STAR Level 1 Certification
RegScale achieved CSA STAR Level 1 certification in August 2024. This self-assessment requires cloud providers to submit the Consensus Assessments Initiative Questionnaire (CAIQ) to document compliance with the Cloud Controls Matrix (CCM). The certification helps users evaluate the security controls of their current or prospective cloud providers.

“As a retired Navy Veteran and lifelong Cybersecurity Practitioner, I’m committed to protecting our security and privacy. At RegScale, we believe security and privacy are fundamental to earning the trust of commercial and federal organizations. Count on us to safeguard your data with integrity and diligence, because your privacy matters most to us.”

Dale Hoak
Director of Information Security, RegScale
Lorem Security
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Nunc urna tellus, venenatis sed massa ac, fermentum porttitor tortor. Donec sit amet velit pellentesque sapien.

Lorem Ipsum Dolor
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt.

Lorem Ipsum Dolor
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt.
Lorem Ipsum Dolor
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt.
Lorem Privacy
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Nunc urna tellus, venenatis sed massa ac, fermentum porttitor tortor. Donec sit amet velit pellentesque sapien.

Lorem Ipsum Dolor
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt.

Lorem Ipsum Dolor
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt.
Lorem Ipsum Dolor
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt.
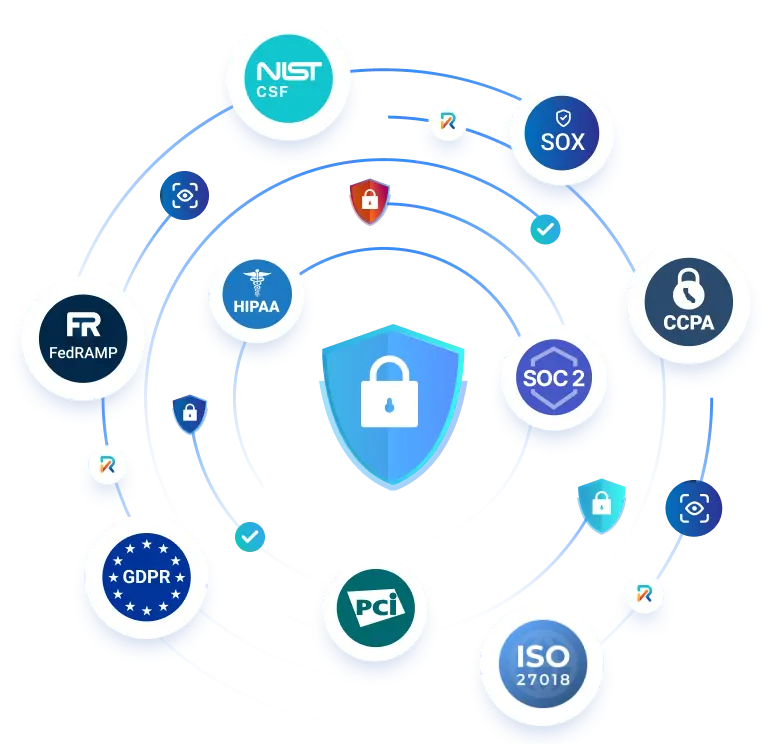
Supporting frameworks across multiple industries
RegScale helps you navigate compliance in a complex landscape where every regulator has their own framework. We provide out-of-the-box support for more than 60 frameworks, and we also partner with regulatory change management platforms for control mapping and content updates.
More Compliance Frameworks

HIPAA
The Health Insurance Portability and Accountability Act, a law protecting the privacy of individuals’ medical records and other personal health information (PHI) in the United States.

CCPA
The California Consumer Privacy Act, a state law intended to enhance privacy rights and consumer protections for residents of California.

NIST CSF
v2.0The National Institute of Standards and Technology Cybersecurity Framework, a high-level taxonomy of cybersecurity outcomes and a methodology to assess and manage those outcomes.

GDPR
General Data Protection Regulation, the European Union’s landmark regulation enforcing data privacy and protection for individuals within the EU.

ISO 27001
v2022, v2013Specifies requirements for establishing, implementing, maintaining, and continually improving an information security management system.

FedRAMP
Rev 4, Rev 5, Baselines High, Moderate, Low, LI-SaaSRisk-based requirements for modern cloud technologies to secure and protect federal information.
Report a Security Vulnerability
If you have found a security issue or vulnerability in the RegScale platform and would like to report it to us, please fill out the following form to report it to our team. Please describe the vulnerability or security issue you wish to report in as much detail as possible.
This form is delivered by HubSpot and requires cookies to load and process submissions.
Ready to fast track your compliance? Let us show you how it’s done
Reading can only get you so far. That’s why we’d like to give you a quick live walkthrough of RegScale to show you exactly what we can do for your organization.
More ways to stay up to date
Get insights delivered to your inbox
Receive platform tips, release updates, news and more
This form is delivered by HubSpot and requires cookies to load and process submissions.